* Enforces trust across Al agents, M2M APIs, and industrial controls
* Controls what systems do, not just what they report
9+
Regulatory frameworks
60-70%
Lower TCO vs. Incumbent Market Leaders
0
Cloud Dependencies Required

“Detection observes incidents. DefenXee makes unsafe execution impossible, by design.”
The DefenXee
Trust Convergence Platform
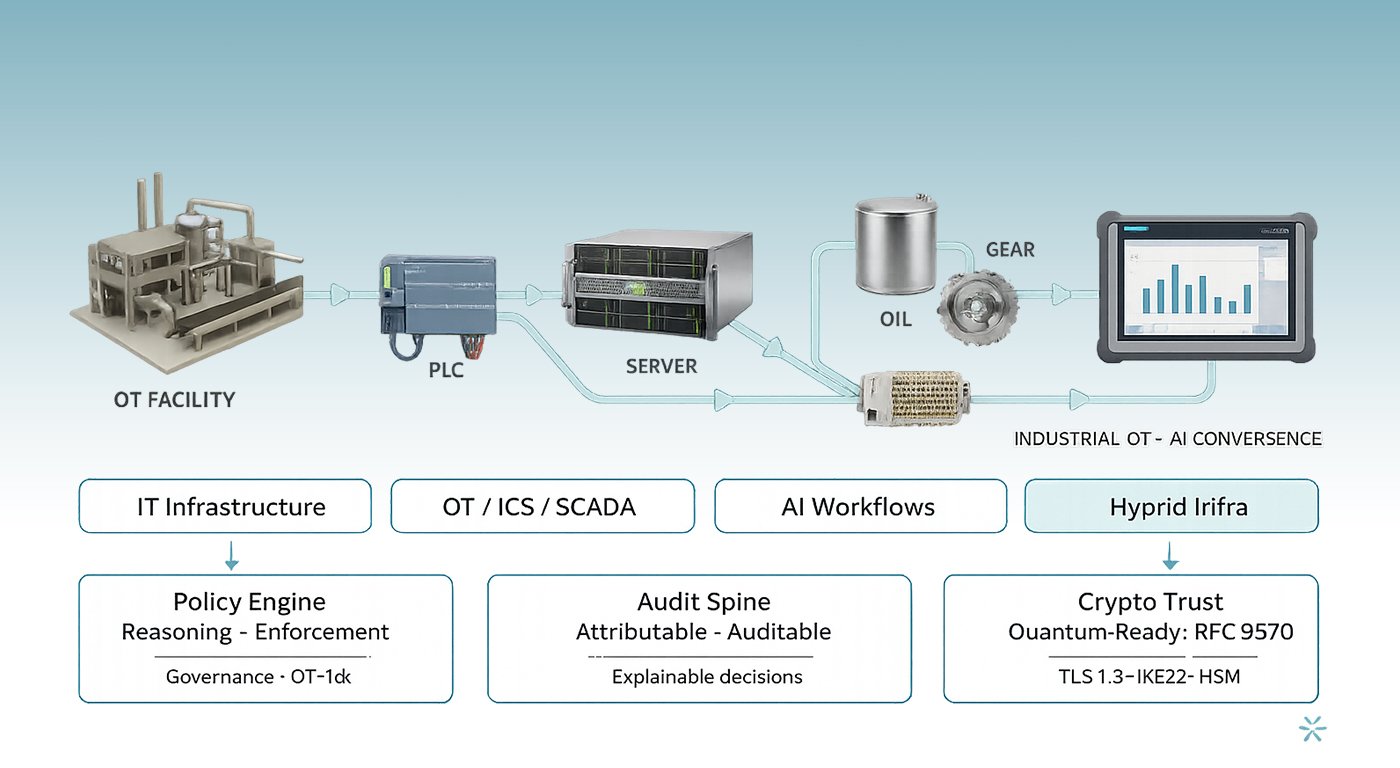
DefenXee brings together governance, policy reasoning, enforcement, and cryptographic resilience into a unified control plane, an industrial cybersecurity platform that protects OT and AI with the same policy engine and audit spine.
Built-in Core Capabilities
AI Governance & Control
Policy-driven reasoning engines that govern AI behaviour and system actions, extending OT cyber risk management into autonomous AI workflows.
Cross-Domain Policy Enforcement
Uniform policy enforcement across IT, OT, AI, and hybrid infrastructures. One engine for your entire industrial cybersecurity platform.
Cryptographic Resilience
Quantum-ready cryptographic trust validation layers. Hybrid TLS 1.3 / IKEv2, RFC 9370 compliant.
Explainable Decision Framework
Machine decisions remain auditable, attributable, and compliant, human-readable rationale on every action for industrial security monitoring and audit teams.
Sovereign Deployment Architecture
On-premise, private cloud, or sovereign infrastructure. No cloud heartbeat. HSM-signed Sovereign Update Protocol. Full feature parity, air-gapped.
Secure Remote Access for OT
OT privileged access management and secure industrial remote connectivity for engineers, vendors, and SOC teams, with full enforcement and audit trail.
Why DefenXee?
Security that Respects Your OT Operations
DefenXee is engineered for environments where uptime is non-negotiable and operational continuity is mission-critical.
Policies defined centrally. Enforced automatically across domains.
Deploys without disrupting operational continuity.
Autonomy within enforceable trust boundaries.
Every decision is attributable, auditable, and explainable.
“Beyond perimeter defence.
DefenXee establishes enforceable operational trust.”
Sovereign by Design, Not by Exception
Trusted Where Failure is Not an Option
Purpose-built for environments where security incidents and production disruptions are unacceptable, not merely manageable.
Runtime enforcement across PLCs, RTUs, HMIs, and SCADA systems. Protocol-deep OT intrusion detection tuned for real plants.
Power grids, water systems, pipelines, and rail networks, where a single unsafe command can cascade into national consequences.
Sovereign trust layers for digital public infrastructure, national payment rails, and classified environments. Air-gap ready.
Solutions by Sectors
Purpose Built for Every Critical Vertical
Runtime enforcement outcomes purpose-built for critical infrastructure verticals.
An ICS cybersecurity solution and SCADA cybersecurity solution that protects IEC-104/DNP3 traffic, substations, and grid automation as a critical infrastructure security platform.
Industrial cybersecurity solutions for signalling, scheduling, and safety automation across thousands of daily services, where failure is never an option.
An industrial cyber protection platform securing SIS logic, pipeline SCADA, and remote compressor stations with OT IDS and OT vulnerability management.
OT cybersecurity solutions and ICS cybersecurity solutions extend industrial network security and OT monitoring across production lines.
Industrial cyber protection solutions that protect treatment plants and distribution networks as part of a national critical infrastructure cybersecurity solution.
CPS security platform capabilities that protect digital ID, payments, and long-lived records against quantum-era threats and autonomous AI risks.
Zone & conduit validation, security levels, and runtime enforcement aligned to the standard.
AI governance controls and decision logging aligned to emerging AI management standards.
Evidence generation and enforcement controls for CIP-002 through CIP-014 requirements.
PII redaction at runtime and decision logs providing data handling transparency.
Information security controls and audit evidence mapped to ISO 27001 clauses out of the box.
High-risk AI system controls, transparency obligations, and logging for EU regulatory compliance.
Incident reporting readiness, audit trails, and enforcement controls aligned with CERT-In directives.
Identify, Protect, Detect, Respond, Recover, runtime enforcement mapped across all five functions.
Security level enforcement and zone-based access controls for industrial automation environments.





